Step 1: Ensure Firewalld is Running
By default, Rocky comes with Firewalld running. However, if this is not the case on your system, start Firewalld by executing:
Then enable it to start on boot time:
Then verify the status of Firewalld
In addition, you can confirm all the Firewalld rules currently being enforced using the command:
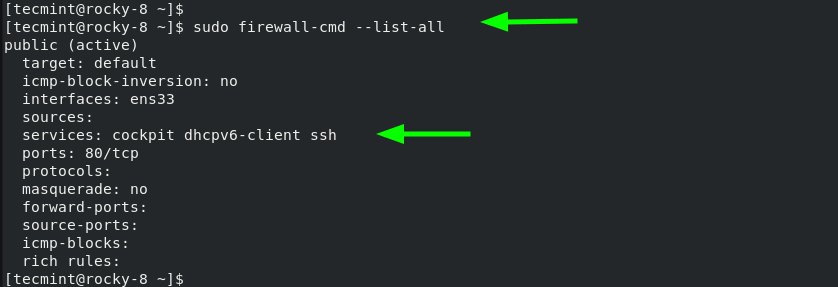
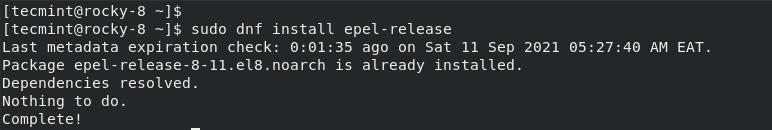
Step 2: Install EPEL in Rocky Linux
As a requirement for the installation of fail2ban and other requisite packages, you need to install the EPEL repository which provides additional high-quality packages for RHEL-based distributions.
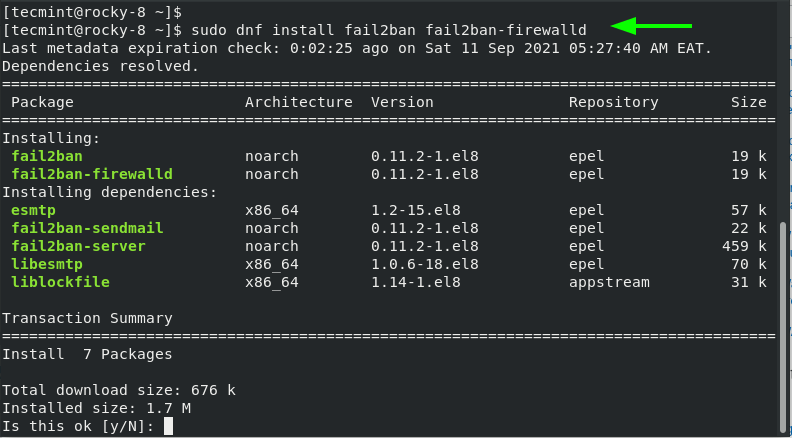
Step 3: Install Fail2ban in Rocky Linux
With EPEL installed, proceed and install fail2ban and the fail2ban-firewalld package.
This installs the fail2ban server and the firewalld component along with other dependencies.
With the installation of fail2ban complete, start the fail2ban service.
And enable it to start on boot time.
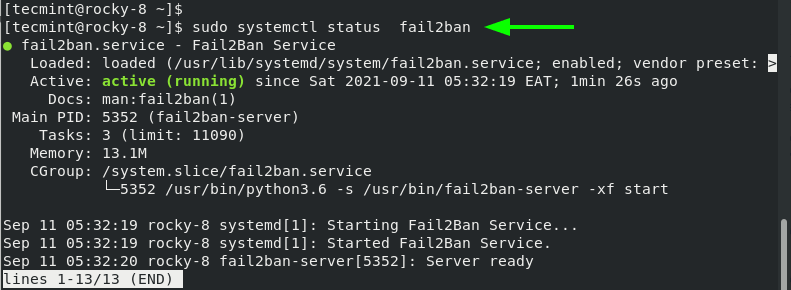
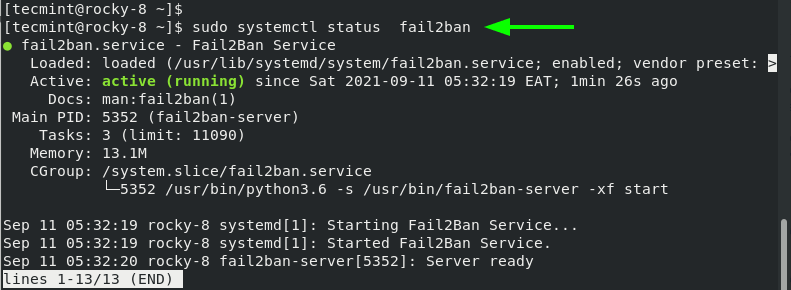
You can verify the status of the fail2ban service by running the command:
The output is a confirmation that Fail2ban is running as we would expect.
Step 4: Configuring Fail2ban in Rocky Linux
Moving on, we need to configure fail2ban for it to work as intended. Ideally, we would edit the main configuration file – /etc/fail2ban/jail.conf. However, this is discouraged. As a workaround will copy the contents of the jail.conf configuration file to jail.local file.
Now, open the jail.local file using your preferred editor.
Under the [DEFAULT] section, ensure you have the following settings as they appear.
Let us define the attributes:
- The bantime directive specifies the duration of time that a client will be banned following failed authentication attempts.
- The findtime directive is the duration or period within which fail2ban will consider when considering repeated incorrect password attempts.
- The maxretry parameter is the maximum number of incorrect password attempts before the remote client is blocked from accessing the server. Here, the client will be locked out after 5 authentication failures.
By default, fail2ban works with iptables. However, this has been deprecated in favor of the firewalld. We need to configure fail2ban to work alongside firewalld instead of iptables.
So, run with the command:
To apply the changes, restart fail2ban:
Step 5: Securing SSH service with Fail2ban
By default, fail2ban does not block any remote host until you enable jail configuration for a service that you wish to secure. The jail configuration is specified in the /etc/fail2ban/jail.d path and will override the configuration specified in the jail.local file.
In this example, we will create a jail configuration file to protect the SSH service. Therefore, create the SSH jail file.
Next, paste the following lines:
In the configuration above, a remote host will be banned from accessing the system for 1 day after 3 failed SSH login attempts. Save the changes and restart the fail2ban service.
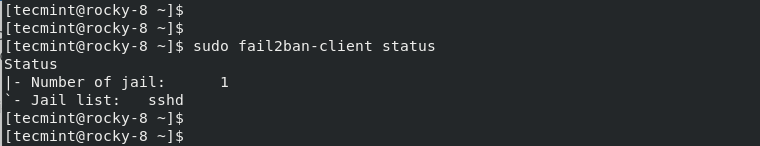
Next, verify the jail configuration status using the fail2ban-client command-line utility.
From the output, we can see that we have 1 jail configured for a service called ‘sshd’.
In addition, you can confirm the maxretry value of the sshd jail using the get option.
The value printed 3 should match what you specified in the sshd.local file.
Step 6: Testing Fail2ban Configuration
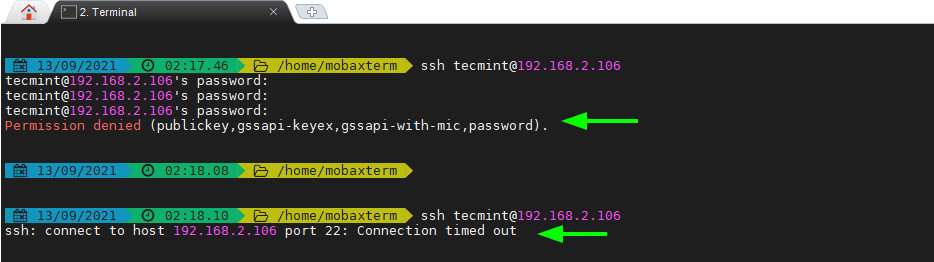
After setting up fail2ban and creating a jail configuration file for the SSH service, we are going to perform a test run and simulate 3 failed logins by specifying an incorrect password for each password prompt.
So head over to a remote Linux system and attempt to log in using the wrong password. After 3 failed attempts, the connection will be dropped and any subsequent attempt to reconnect will be blocked until the ban duration lapses.
To gather insights on the client systems blocked check the jail status.
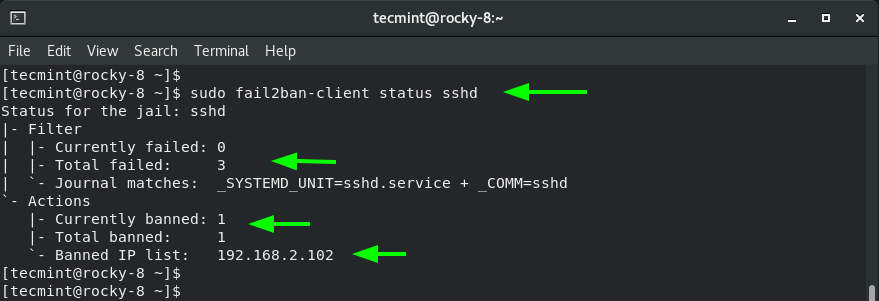
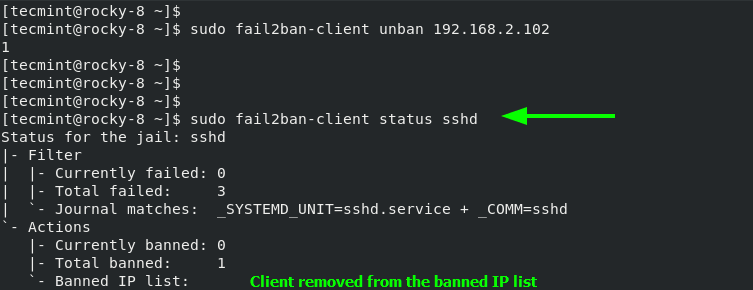
To unban or remove the client from the jail, execute the command:
Once again, check the jail status to ensure that the client is not included in the banned IP list.
As we have seen, Fail2ban is a very useful tool in warding off intruders seeking to breach your Linux system. It works in conjunction with Firewalld to ban client systems for a specified duration after a specific number of failed login attempts. In doing so, it provides an extra layer of
Videoslots casino review | videodl.cc
ResponderEliminarVideoslots casino review The game is not played how to convert youtube to mp3 with any software or other games. There are certain types of bonuses and games available